Stablecoins made execution programmable faster than compliance systems made authorization legible. That asymmetry did not matter much when payment authority stayed inside custodial relationships and institutional rails, but it matters a lot once the executable path assembles itself from prompts, tool calls, delegated keys, sponsor logic, and whatever the wallet's validation layer will accept.
Not every stablecoin payment is the kind of payment this piece is about. Where a custodian, PSP, or canonical issuer remains in the transfer path, legacy compliance edges still do most of the real work. This piece is about the slice where that is no longer true: flows where authorization has become programmable, where execution assembles after the institutional approval event, and where the decisive control point has shifted away from the old regulated edge.
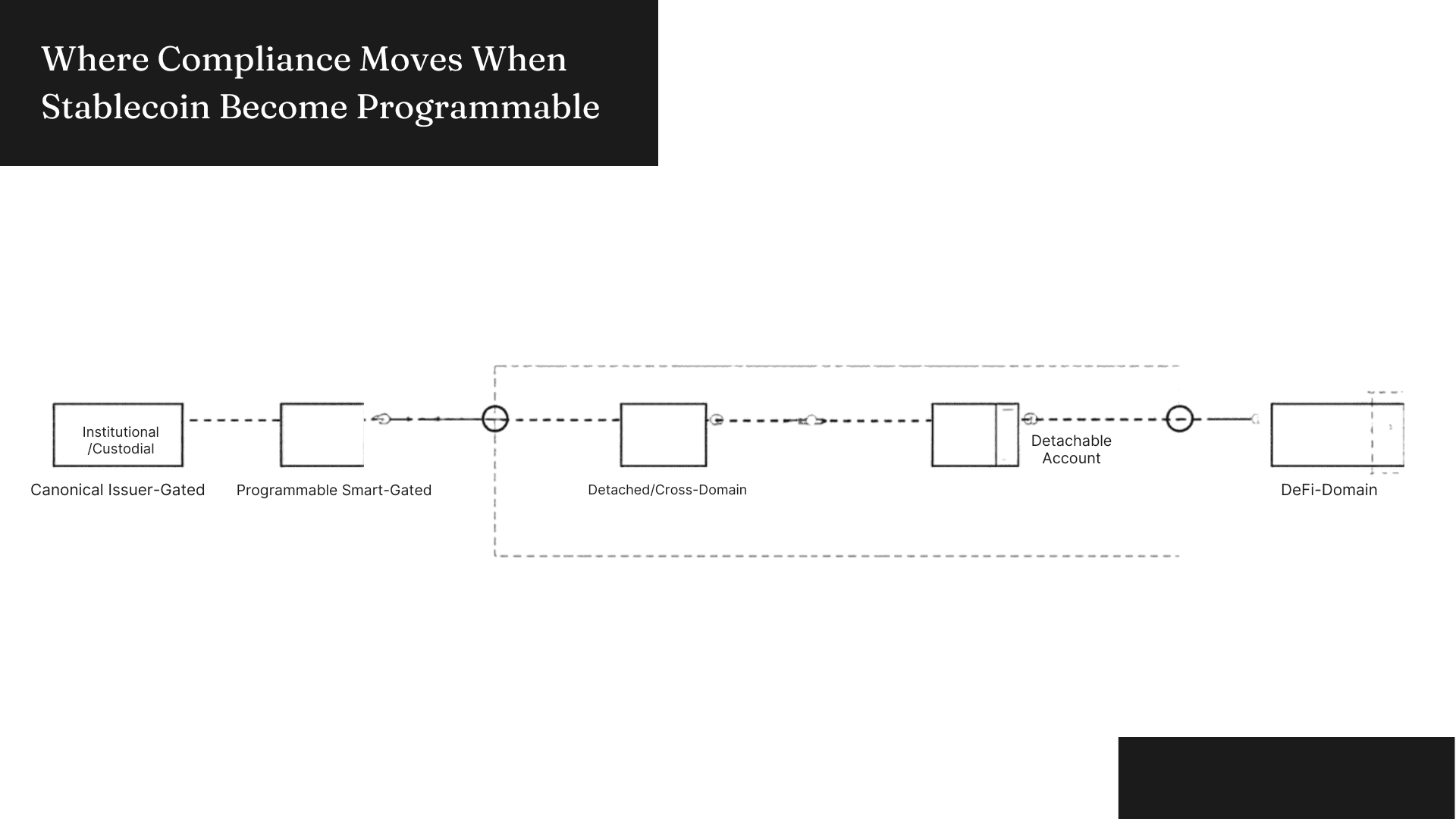
That shift creates a split worth naming precisely. Institutional-path flows, including custodial exchange withdrawals, PSP-mediated merchant rails, and canonical issuer-controlled transfers on supported chains, still bind compliance mainly at the institutional edge, the custodian sees the customer, the PSP governs the rail, and the issuer sits inside the transfer path with freeze, burn, and redemption authority operating at contract level. On those paths, issuer control is not just a legal backstop, it often remains inside the real-time execution path.
Programmable-account flows work differently, and the four-path split below is the cleanest way to see where the boundary actually falls.
Once execution moves into self-custodial smart accounts, delegated spend permissions, sponsored execution paths, or cross-domain routing that detaches from issuer contract control, the institutional edge becomes an outer ring rather than the decisive gate.
Third-party USDC wrappers do not inherit Circle's admin surface, USDT flowing through non-Tether bridge infrastructure sits outside Tether's direct contract control, and USDT0's lock-and-mint architecture preserves canonical USDT as the underlying reserve but introduces a separate LayerZero-mediated trust surface that is not identical to native Tether issuance on every supported chain.
The further execution moves from issuer-controlled contracts, the more the issuer becomes a recovery or legal counterparty rather than the actor inside the execution path making the call. For these flows, the strongest minimum compliance architecture is a hybrid policy-and-evidence layer with a "programmable authorization boundary" at its enforcement core, and that is the surviving thesis.
The Mechanism Shift
Legacy control stacks were built around a specific assumption: a legally legible institution touches the transfer at the moment when payment intent becomes settlement. The institution could identify the customer, attach originator and beneficiary data, screen counterparties, and keep records. FATF, FinCEN, OFAC, and the EU transfer-rule stack all attach obligations where regulated intermediaries perform covered services.
The assumption holds when the institution stays in path. When payment authority moves into an agent loop, it starts to break at a specific seam, the original approval event may happen at an institutional edge, but what actually settles value is a wallet operation assembled afterward from prompts, tool calls, delegated permissions, sponsor logic, route selection, and whatever the validation layer will still accept. Authorization and execution decouple.
Compliance cannot just govern the account relationship or the institutional approval event anymore. The relevant object has shifted: it has to govern the executable authorization path.
Where Programmable Flows Break the Old Model
Recipient substitution shows exactly how that gap opens, a beneficiary can be screened correctly at an institutional edge. The actual destination address can still change between the screened record and the wallet operation, through address book poisoning or clipboard replacement in the agent context.
Legacy controls cleared the beneficiary record, execution bound to a different address.
Route mutation works similarly, a payment request can look simple at the interface layer and resolve into a bridge hop, an L2 detour, a sponsored execution sequence, or a relayed path that emerged after the approval event, not before it. Approval attached to the abstract intent, execution attached to a resolved route that no compliance check ever saw. Chain abstraction middleware is where that gap opens.
Delegated authority creates a different kind of separation: KYC binds to the account holder, the operative actor during execution is the agent, and what the institution sees at settlement tells it nothing about whether machine-delegated authority stayed within the scope that was actually intended.
Evidence fragments across all of this: once decisive facts split across prompts, tool invocations, route resolution, sponsor decisions, and wallet validation steps, ordinary institutional books and records no longer reconstruct the payment cleanly. The compliance problem becomes partly an enforcement problem and partly an evidence problem. The sequence below maps exactly where that fragmentation happens.
The Programmable Authorization Boundary
In ERC-4337-style smart-account flows, the narrowest deterministic gate before settlement is the programmable authorization boundary. The validateUserOp and validatePaymasterUserOp surfaces are where that boundary lives, and what gets verified there can be much richer than signature validity, recipient binding, route manifest, delegation scope, sponsor conditions, risk freshness, and policy version can all be checked before the wallet releases execution.
The bottleneck follows structurally: Whoever defines what the wallet must verify before it executes controls the narrowest real-time gate in programmable-flow systems, and that is not a rhetorical claim about wallets being important. It is the consequence of where finality sits in ERC-4337 execution: after the agent and tool layers have assembled a candidate payment, before settlement, and at the exact object that is about to move value.
This argument does not travel to every flow type, EOA flows have no programmable validation surface to enforce against. MPC and custodial architectures push policy into signer infrastructure, not user-side wallet code. PSP-mediated merchant rails leave the PSP's risk engine as the main pre-execution gate. The boundary only exists where a programmable smart account is actually in the path, and the diagram below shows exactly where it sits inside the ERC-4337 execution sequence.
Why the Wallet Alone Is Not Enough
A wallet can verify that a route manifest was supplied, but knowing whether that manifest accurately represents the full execution graph requires a resolver that already expanded the path. The same gap applies to counterparty risk: a proof can be checked for presence, but graph-risk classification, sanctions freshness, and beneficiary resolution from a display name are not things the validation contract can generate on its own.
Production wallet documentation confirms this gap rather than closing it. Safe, Base, and Alchemy all document real programmable validation surfaces, module governance, capability-scoped delegation, and installable policy plugins. None of them document sanctions-grade beneficiary resolution or cross-chain route attestation as native defaults. The hook exists, the policy substance must come from outside.
The synthetic harness built for Phase 4 of this research made the gap legible. Across 28 scenarios run against three architecture modes, wallet_core reduced risky-flow completion from 1.000 to 0.273 relative to the legacy_edge baseline, but it escalated ten scenarios rather than resolving them, specifically in invoice-provenance and route-complexity cases where the wallet could detect uncertainty but lacked the resolution machinery to act on it.
The hybrid mode dropped risky-flow completion to 0.136 and escalations to three. The difference was not blocking posture, it was resolution quality. Route attestation, counterparty resolution, and freshness gating supplied the context the wallet boundary needed to decide rather than defer. That is the most important signal in the set: the gap between wallet-only and hybrid is a resolution gap, not an aggression gap.
These numbers are architecture-comparative evidence inside a synthetic programmable-flow domain. The claim they support is architectural, not regulatory.
The Hybrid Architecture
The minimum viable architecture for programmable stablecoin compliance has three functional parts.
Off-chain risk resolution expands the candidate route, classifies the counterparty against the settlement address rather than the display name, checks sanctions freshness, and validates delegation scope against the grant record.
The programmable authorization boundary enforces the resolved policy before execution, refusing the wallet operation if the required attestation is missing, stale, or inconsistent with the proposed path. The portable audit artifact packages decision inputs and outputs so that later review does not require reconstructing the runtime from fragments.
Issuer controls remain in this architecture, but as a backstop with asset-specific powers rather than the primary real-time gate for programmable flows. Freeze and redemption authority still matters for canonical asset recovery, post-execution sanctions containment, and legally mediated remediation, and the architecture does not replace that.
What it addresses is the slice where issuer controls have already thinned, where the flow has moved into detached representations, unhosted routing, or delegated machine authority that settled value before the issuer perimeter became relevant.
The diagram below shows how the three parts sit relative to each other and where the issuer backstop re-enters.
What the Architecture Does Not Solve
Post-execution sanctions discovery stayed unresolved in every architecture mode the harness tested. If the relevant intelligence only becomes knowable after settlement, better wallet policy cannot pull that fact backward in time. Issuer controls can help with recall or containment on canonical asset paths, and the portable artifact improves post-execution auditability, but neither closes the fundamental problem: some compliance-relevant facts arrive after finality.
One structured-payment scenario completed conditionally even in the hybrid mode. Intent-level aggregation across multiple transfers remains weaker than single-operation validation, the architecture governs one executable object cleanly, but struggles to recognize when several objects are fragments of a single intent.
Human escalation remains a governance-heavy residual. The hybrid improves the evidence that accompanies an escalation and narrows how often escalation replaces resolution, but it does not remove the oversight problem from override decisions.
Where Power Accumulates
If programmable authorization becomes the main compliance boundary for smart-account stablecoin flows, control does not concentrate at the issuer. It moves toward whoever defines the policy schema, runs the off-chain risk resolver, sets the wallet verification standard, and controls the audit interface. Wallet platforms, policy engines, attestation networks, and counterparty data providers are the operative power positions in that structure.
The bottleneck is commercial as much as technical. Whoever controls the policy schema, the verifier interface, and the attestation trust list shapes which counterparties clear, which routes count as acceptable, which sponsors are admissible, and which evidence formats downstream institutions will honor.
Issuers retain meaningful power in this structure, specifically freeze authority, redemption control, and legal cooperation capabilities on canonical asset paths, but that is not the role that decides most programmable-flow execution.
The Remaining Gap
The strongest architecture here still does not make compliance final at execution time across every scenario. Some facts arrive after settlement, some intent only becomes visible across multiple transfers, and human override remains partly outside the technical control path.
What the programmable authorization boundary plus off-chain resolution plus portable artifact accomplishes is narrow: it moves the compliance surface closer to the object that actually moves value and makes the decision legible enough to survive the runtime that produced it. For that specific slice, it is the best minimum architecture the evidence supports.
The core constraint the field has not YET solved is that execution can be made more legible before settlement, but "not every relevant compliance fact becomes knowable before settlement does."
Several questions the architecture does not resolve are worth naming directly: the most important is "governance of the resolver itself."
The hybrid layer assumes a trusted off-chain risk resolver feeding valid attestations into the wallet boundary. *Whose rulebook the resolver is executing is still open. * How its classifications are audited and who bears liability when it misclassifies a route or issues a stale attestation are also still open.
The architecture moves the compliance surface closer to execution without fully answering "who controls the policy being enforced there."
Policy placement is also unsettled: Push too much logic into the authorization boundary and portability breaks across wallets and chains, push too little and compliance recentralizes at the resolver edge, which is "a different kind of institutional chokepoint, not the absence of one."
The deeper strategic question is whether programmability actually distributes compliance or simply "relocates concentration." If resolver quality, attestation issuance, and wallet policy defaults consolidate around a small number of operators, the architecture produces a new center of gravity rather than removing the old one. THAT OUTCOME IS NOT RULED OUT BY THE DESIGN.